A VLAN (Virtual Local Area Network) is a fundamental concept in TCP/IP computer networks and every professional in this field must have a deep understanding of this technology.

In networking, VLANs are implemented and configured on Ethernet Switches and they work at OSI Layer 2.
They are a method to logically separate Layer 2 Ethernet Frames generated by different devices in the network so that only frames having the same VLAN ID can communicate in Layer 2.
Frames with different VLAN ID must pass through a Layer 3 device (e.g router) in order to communicate.
Therefore, using a Router (or Layer 3 Switch) we can control the traffic between different VLANs (e,g using Access Control Lists).

This separation of frames (and thus devices) adds to the security of the network by segregating the traffic from different devices so that they can only communicate at layer 2 with devices that have been assigned the same Vlan number.
VLAN Range
Vlans are identified by numbers that range from 1 to 4094. There are some reserved numbers within this range, and these are as follows:
- 1003 to 1005 – reserved for Token Ring
- 1 to 1005 Normal range
- 1006 to 4094 – Extended Range
Ethernet Frame Structure
Different VLANs are identified by a tag that is placed within the ethernet frame. This tag is called the 802.1Q tag and is sometimes referred to as a Dot1Q tag.
The layout of a standard ethernet frame that has not been assigned a Vlan tag is shown below:
| Destination MAC Address | Source MAC Address | Length / Type | DATA | FCS |
The layout of an Ethernet Frame that has a VLAN assigned with a 802.1Q tag is shown below:
| Destination MAC Address | Source MAC Address | 802.1Q TAG | Length / Type | DATA | FCS |
Importance of VLANs for Network Segmentation
Security
As an example, all the devices that belong to the Finance department could be assigned VLAN 10 and all the devices that belong to the Research department could be assigned VLAN 20.
For security reasons, as these are different departments, a computer in the Research department should not ordinarily be able to communicate with a computer in the Finance department and vice versa.
The VLAN assignment is configured on the interfaces of the switch that the computers are connected to. The switch therefore will insert a VLAN ID tag to each Ethernet frame coming from the computers.
The switch only allows Layer 2 communication to flow between the interfaces that have the same VLAN Assignment.
This means that no Layer 2 communication will occur between the computer in the finance department and the computer in the research department because of their different VLAN assignments.
Smaller Broadcast Domains
VLANs often span across multiple network switches, if a single VLAN is assigned to all the switch interfaces then this would create a single large broadcast domain.
By segregating switch interfaces into different VLANS this large broadcast domain gets divided into multiple smaller broadcast domains.
The more VLANS that are added the smaller the broadcast domains will become and the more broadcast domains there will be.
Because each VLAN has its own broadcast domain this makes it possible for each VLAN to have its own instance of Spanning Tree. This is known as Per VLAN Spanning Tree (PVST).
Better Network Management
VLANS are a good way of organizing devices which have similar roles into logical groups and because VLANS can span across multiple switches in a network these similar devices can be physically separate but reside in the same logical grouping.
This logical organisation can help to simplify the configuration and management of devices within a large network.
VLANs on Cisco Switches (VLAN Database)
When a new VLAN is created on a switch the new VLAN is recorded in a database. This database is stored in the NVRAM or flash memory in a file called the vlan.dat file.
To view the contents of the Vlan database on a Cisco switch the command show vlan is used.
If the Vlan.dat file is deleted from the switch then all configured VLANS will be lost, and the database will be set to its default configuration.
To delete the vlan.dat file the command delete flash:vlan.dat can be used. For security it is advised to make a backup copy of the vlan.dat file so that the VLAN database can be recovered if needed.
There is a protocol called VLAN Trunking Protocol (VTP) that can be used to ensure that every switch on the network has the same VLAN database.
This Protocol requires a switch to be configured as a VTP server, and all other switches are configured as either Transparent switches (no VTP) or Client switches.
When a change to the Vlan database is made on the VTP server switch, it sends out a VTP message which updates the VLAN Database of all the Client switches.
For extended VLANs to be used from the range 1006 to 4094 the switch must be configured with the Transparent VTP mode.
VTP should be used with caution as it is possible to wipe all the VLANS configured on a network if a new VTP server is added by mistake.
Let’s now describe and discuss the different Types of VLANs in networking:
Default VLAN
When a Cisco switch arrives from the factory and is first powered on, all the interfaces are placed in VLAN 1, which is the default VLAN on Cisco Switches and for most other switch vendors.
Interfaces that are assigned in the default VLAN do not tag the Ethernet frames as they leave the Interface, so all connected devices that are assigned the default VLAN will be able to communicate with one another.
VLAN 1 is always up on a Cisco switch, and it cannot be deleted. VLAN 1 is primarily used for internal Layer 2 control traffic within the switch such as Spanning Tree messages or CDP and this cannot be changed.
Network administrators sometimes refer to the VLAN which has been assigned for interfaces that are not in use as the default VLAN which can be confusing as this is not really a default VLAN, but a VLAN that has been chosen for the assignment of empty interfaces as a security best practice.
By putting unused interfaces into separate VLANs on the switch this prevents unauthorised access to a data VLAN should someone plug a laptop into an empty interface.
Native VLAN
Multiple Switches are connected by using Trunk interfaces. Unlike a standard Access interface which only has the ability the pass traffic for the one VLAN that has been assigned to it, a trunk interface is able to pass the Ethernet frames from multiple tagged VLANs.
This is known as 802.1q Trunking. The trunk not only passes tagged frames across its link but also untagged frames such as control traffic or traffic from legacy devices which are unable to tag their Ethernet frames.
All this untagged traffic by default is put into VLAN 1 which is the native VLAN. There is a difference between a native VLAN and the default Vlan because the native VLAN can be and is often assigned another number.
The important thing to remember is the native VLAN can be whatever number you want to use within the range of 1 and 4094 but the native VLAN number must match on both interfaces which connect the trunk.
You cannot have a native VLAN of 2 on one side then a native VLAN 3 on the other side as this will cause a mismatch and communication across the trunk will fail.
The command to change the assigned native VLAN of a trunk on a Cisco switch is as follows:
switchport mode trunk
switchport encapsulation dot1q
switchport trunk native vlan <vlan number>.
To check which native VLAN a trunk port has been assigned, the following command should be run on both sides of the trunk link:
show interface GigabitEthernet 0/1 trunk
Management VLAN
A management VLAN is created for the purpose of managing just infrastructure devices using SSH, HTTPS, SMTP or SYSLOG etc.
The VLAN number can be any that the Administrator wants to use. For the devices in this VLAN to be reachable for management from a remote computer, a Switch Virtual Interface (SVI) needs to be created on a Layer 3 device such as a Router or Multi-layer Switch and assigned an IP Address.
All the devices that need to be managed also need an IP address to be assigned in the same IP subnet as the SVI.
To keep things simple and easy to remember the third Octet in the IP range often matches the number given to the VLAN (just as best practice).
For example, if the management VLAN was VLAN 10 then the IP address assigned would be 192.168.10.1 /24 for the SVI.
All devices that needed to be managed would then be assigned an IP address from this same IP address range such as, 192.168.10.10 /24 or 192.168.10.11 /24.
It is a best practice to separate management traffic from user data traffic and the management VLAN is used for this purpose.
Data VLAN
The data VLAN is where end user devices are assigned. There can be many Data VLANS which can be numbered or named to represent different departments or groups of devices.
There could be a VLAN called Finance, then a VLAN called Sales and then another VLAN called Research.
A VLAN could be created for different devices such as a VLAN called Phones or a VLAN called AV which just contains Audio and Video devices.
Voice VLAN
Usually in an office environment each desk will have a computer and an IP phone. To connect both the IP phone and the computer to the switch separately would require 2 cables to be ran from each device to the switch.
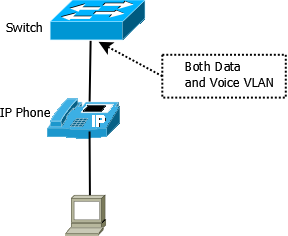
In a large office the number of free interfaces on the switch would quickly become depleted so Cisco created IP phones that have a mini switch built into the base unit of the phone.
This mini switch allows the PC to connect to the phone and then traffic from the PC is forwarded by the phone through a single Ethernet connection to the Cisco switch (see diagram above).
The problem with this is that ordinarily a switch interface that is configured with switchport mode access can only accept a single VLAN on the interface.
To overcome this problem, Cisco switches allow a standard Data VLAN to be assigned to the switchport which would support the computer and then a Voice VLAN can also be added to support a Cisco IP phone.
When the IP Packets leave the phone, they will be tagged with voice vlan for the IP phone or data VLAN for packets originating from the computer.
The commands to configure both a voice vlan and a data vlan are as follows:
switchport mode access
switchport access vlan 10 (DATA)
switchport access voice vlan 101 (VOIP)
Tagged and Untagged VLAN/port
Packets can either be tagged with a dot1q tag or not tagged at all.
Quick Summary:
- Tagged Port: Called also “Trunk” port in Cisco. Packets must have a VLAN tag. This port accepts traffic from multiple VLANs. Usually used to connect switches together.
- Untagged Port: Called also “Access” port in Cisco. Accepts traffic only for a single VLAN. Usually used to connect end-devices to switches.
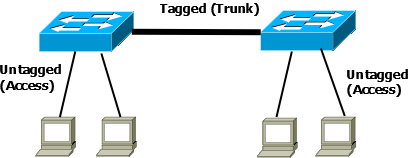
Some end devices can tag the packets leaving the device with a dot1q tag whereas most others do not have this ability.
So, when the packet reaches the switch, depending on what type of interface the device is connected to, the switch will have a bearing on what happens to the tagging within the packet.
If a tagged packet leaves a device and reaches the connected interface of a switch that has been configured as an Access interface, the switch checks that the tag is the same as the allowed VLAN assigned to that Interface. If it matches its allowed to pass if it doesn’t match, then it gets dropped.
If the packet that is sent from the device is not tagged, when it reaches the same interface it is treated as Untagged and given a new tag which matches that of the VLAN assigned to the interface.
An Access Interface is an UNTAGGED interface which only allows a single VLAN to pass. A Trunk interface is a TAGGED interface which allows packets tagged with multiple Vlans to pass and untagged packets are assigned the VLAN ID tag of the Native VLAN for that Trunk Link.
Private Vlans
Private VLANS are a way of isolating devices which are in the same VLAN by assigning them a secondary vlan that is designated as either a Community Vlan or an Isolated Vlan.
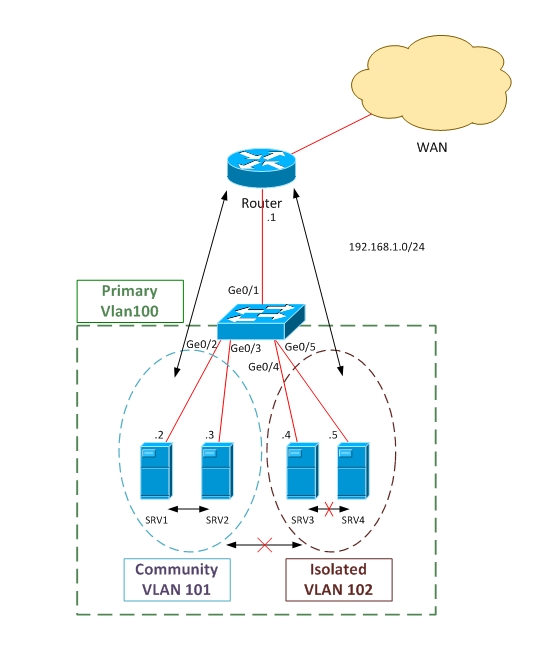
A switch which is configured for private VLANs will have interfaces which are assigned to a primary Vlan number.
Within this group of interfaces, one will be configured as a promiscuous port. This promiscuous interface can communicate with any other interface and any other interface can communicate in return.
The Interfaces which have been configured as a community interface can communicate with all other interfaces which have been configured in the same community VLAN and they can also communicate with the promiscuous interface.
Interfaces which have been designated as an isolated VLAN can only talk to the promiscuous interface.
If a server was connected to the promiscuous interface, it would be able to talk to all the devices within the same private VLAN both Isolated and Community assigned interfaces.
A Server connected to a community interface could talk to the promiscuous server and any servers connected to another community interface (with same community VLAN), but it could not talk to any servers which are connected to an isolated interface.
Private Vlans can be useful when different companies are sharing the same resources, but you want to keep Company A separated from Company B.