I’ve been working with small and large networks for almost two decades. I can say that I have pretty much seen it all.
There are so many different types of network devices that you can write a whole book about.
In this article I will describe briefly the most common network device types that you will find in most modern corporate networks around the world.
Networks might not have all the devices listed below but in large enterprise networks you will find most of them.
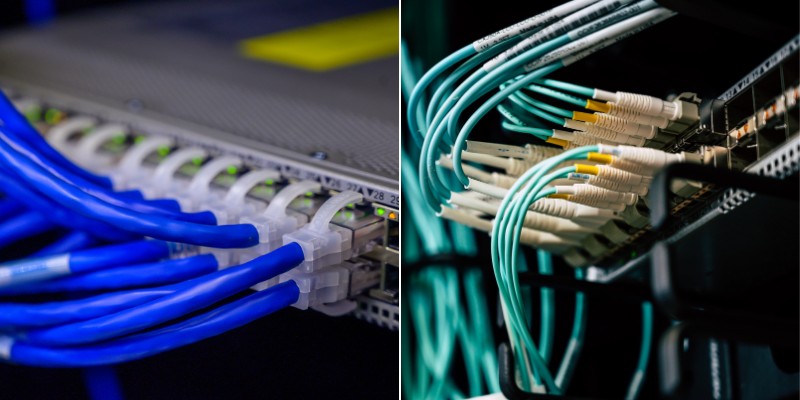
Layer 2 Switches
These types of switches are usually found at the Access layer of a LAN network where the End User devices such as Computers, IP Phones and other network hosts are connected.
They are known as Layer 2 switches because they only operate at Layer 2 of the OSI model, which is the Data Link layer.
Layer 2 switches make all of their packet forwarding decisions based on MAC Addresses that are stored in the MAC Address table of the switch.
The MAC address table in a Layer 2 Switch maps the unique MAC Addresses of devices to the interface that these devices are connected to.
Layer 2 Switches use VLANs to segregate network traffic and because there is no Routing table or IP routing services available to a Layer 2 Switch, devices connected to interfaces assigned to different VLANs will be unable to communicate with each other.
Devices that need to communicate to each other in different VLANs will need to have their traffic sent upstream first to be routed to the other Vlan by a Layer 3 device such as a Layer 3 switch or Router.
Layer 3 Switches
A Layer 3 Switch is both a Layer 2 Switch and a Router combined into a single device. A Layer 2 Switch and a Layer 3 Switch will often look identical from the outside, but a layer 3 switch will have routing capabilities (just like a normal router) in addition to having multiple access ports for connecting hosts to the LAN.
A Layer 3 Switch is used at the Core or Distribution layer of the network where all the Layer 2 Access switches and servers often connect back to.
A Layer 3 switch can use a MAC address table to forward traffic to devices that are directly connected in the same way as a Layer 2 switch, or it can forward packets to other networks by checking entries in its IP routing table against the packet’s destination IP address.
Layer 3 switches enable devices in different Vlans to be able to communicate by routing the traffic between the Vlans (also called “Inter-Vlan routing“).
This is achieved by creating SVI’s (Switch Virtual Interfaces) and by assigning IP addresses from different subnets to these SVI’s. They are then seen as different networks in the Layer 3 Switches routing table and traffic can be routed between them.
Routers
Routers are purely Layer 3 devices and operate at the Network layer of the OSI model. Routers are often found at the point in the network which connects to the Service Providers Wide Area Network (WAN) and these devices route IP packets to different networks based upon the entries found in its routing table.
Unlike a layer 3 switch, there is no MAC address table in a router as a router does not make forwarding decisions by reading MAC Addresses, only IP addresses.
A router will have different interface types and not just Ethernet like a switch.
For example, a router may also have an RJ11 interface which connects to the phone line and uses the router’s internal modem for ADSL connections.
Some routers also provide other services such as Wireless modem or IP telephony. These types of routers are called Aggregated Services Router (ASR) or Integrated Services Router (ISR).
Network Load Balancer Device
A Network Load Balancer is a device that is often found in Server farms or data centres. A Network Load Balancer operates at Layer 4 of the OSI model which is the transport layer and is responsible for keeping track of TCP sessions.
As the name suggests a load balancer evenly distributes traffic received on an incoming interface towards two or more other devices.
A load balancer will help prevent application or web servers from overloading by distributing traffic between many different servers hosting the same application or website.
Examples of companies that supply load balancers are F5, Barracuda and Sonicwall.
Network Firewalls
A Network Firewall is a physical device that inspects IP packets as they flow in or out of the network and allows or denies access to those packets by comparing them to a set of preconfigured rules from top to bottom (called “Firewall Policy Rules”).
When a rule is matched the packet is either forwarded or dropped. There are two types of network Firewall and these are a Stateless Firewall and a Stateful firewall.
A Stateless firewall is very basic and does not carry out deep inspection of the traffic flows or individual packets.
A Stateless firewall will simply look at the packets header and make the decision to forward or drop the packet based on the Source or Destination IP address of that packet.
A Stateful firewall carries out deeper inspection of both the individual packet and the whole traffic flow or conversation between devices as it keeps track of all the individual sessions flowing in and out of the device.
Some Stateful firewalls are more advanced than others and are able to carry out much deeper inspection of the traffic or carry out encryption services such as VPN tunnelling or Network Address Translation (NAT).
A Next Generation Firewall such as a Cisco Firepower or Palo Alto firewall is an example of an advanced Nextgen firewall, and these kinds of devices have many security features built into them which allow far more detailed and granular rules to be created.
Rules can be created to only allow access in and out of the network to certain applications from certain source addresses or URL filtering can be used to prevent End Users from web browsing to known malicious websites.
Network Intrusion Detection / Intrusion Prevention System
A Network Intrusion system looks for known malicious signatures in packets and in network behaviour to determine if there is malicious activity in progress.
A Network Intrusion Detection System (IDS) is used to alert the Network Administrator when potentially malicious behavior or anomalous (unusual) behavior is detected within the network. The IDS just creates alerts but does not actually block the malicious network traffic.
An Intrusion Prevention System (IPS) on the other hand, not only alerts the Network administrator of malicious behavior, but it can also take action to mitigate the malicious behavior by instructing other devices in the network to take action.
Firewalls for example can be instructed to block the traffic flow or by shutting switch interfaces.
Both the Network Intrusion Detection and the Intrusion Prevention System need to learn what is normal network usage and create a baseline.
When these systems are first implemented they often generate many alerts for normal network behavior. These alerts are called false positives, so there must be a period of learning-phase in order to train the system about normal behavior or actually malicious behavior.
Network WAF (Web Application Firewall)
A Web application Firewall sits between the internet and a Web server and filters HTTP traffic destined for the Web Application running on the server.
This type of firewall only has a single purpose which is to protect the Web Application from threats such as SQL injection, cross site scripting and other Web related attacks, and therefore does not have many other features.
There are three methods of deploying a web application firewall. The method chosen depends mainly on affordability.
A physical hardware appliance is the most expensive method, the next is software based and resides on server system and the final and most economical is a cloud-based solution such as CloudFlare or Akamai, however you have less control over a cloud based solution as it is managed by a 3rd party.
Network Database (DB) Firewall
A Network Database Firewall protects access to the information stored within a database server system by monitoring for suspicious database requests or attempts by an unauthorised system to exfiltrate data.
This type of firewall prevents attacks such as SQL injection or buffer overflow attacks by scanning the incoming requests for known malware signatures.
Generally, Network Database Firewalls are physical devices that have been security hardened and are implemented in the traffic path towards the Database server or a software application that runs on the same server as the database.
The physical device is used in most cases as it does not place any additional strain on the processing power of the database server.
Secure Email Gateway Devices
Emails are often used for phishing attacks which attempt to dupe the recipient into clicking on links to malicious web sites where they can unwittingly give away personal information or passwords which can then be used to carry out attacks on a network such as deploying backdoors or doing lateral-movement attacks.
A Secure Email Gateway blocks emails that are sent from domains which are untrusted or have a poor reputation preventing most phishing emails from reaching the intended targets.
Emails are also scanned for malicious content embedded in images or attachments.
Network Sandbox devices
A network sandbox device monitors the network for suspicious files and automatically quarantines these files into a protected environment where the code within the file can be analysed further without the risk of the Malware spreading to other devices within the network.
Sandboxes are often virtual machines that run independent from the underlaying host operating system.
When a suspicious file is found (e.g an attachment in an email), it can be sent to a sandbox network device which actually executes the suspicious file in an isolated “sandbox” environment in order to verify if the file is harmless or not.
Network Wireless LAN Controllers (WLC)
A Wireless LAN Controller (WLC) connects the Wireless Network to the Wired Network and manages the traffic generated by wireless clients and Access Points.
These Wireless Clients use radio waves to communicate over the air to Wireless Access Points (WAP).
A Wireless LAN controller has the ability to manage hundreds of Access Points at the same time and it is from this device that each WAP receives its configuration.
An access point that is attached to a controller is known as a LightWeight Access Point and only has a very basic operating system installed.
All settings, such as which SSID should be broadcast or which radio channel to transmit on, are all determined by the Wireless LAN Controller.
The Wireless LAN Controller can be a physical device such as a Cisco 9800L or it can be a Virtual Machine running on a VMware server.
There are also WLC’s such as Meraki which receive all of their wireless configuration from controllers that are software based and hosted in the cloud.
WiFi Access Points
A Wireless Access Point is a device that provides network access to End devices such as mobile phones or laptops over the air by using electromagnetic radio waves.
There are Access Points which require connectivity to a Wireless Lan Controller to function called Lightweight Access Points (LWAPS) or Access Points that have the controller built into them as software and are known as Mobility Express or Autonomous Access Points.
Access Points that require a Controller usually connect to an Access switch and the traffic from the Access Point to The WLC is carried over the network in an encrypted tunnel called a CAPWAP tunnel.