The most common attack against Service Provider IP Networks is Denial of Service. Usually these attacks take the form of “Many-to-One Attacks” where multiple attacking sources send flooding traffic towards a single destination. These attacks are sometimes called Distributed Denial of Service. Usually the attacking hosts are “zombie” computers which are compromised by hackers and belong to a BotNet network. Usually these attacks are directed towards a critical node of the ISP network (a Border Router, a public Server etc).
If the attack contains thousands of non-legitimate connections to initiate TCP communication (SYN packets) towards a single host, the target host gets overloaded from the requested connections because the three-way TCP handshake does not get completed (because these TCP connections have unreachable return addresses, the connections cannot be established). The resulting volume of unresolved open connections eventually overwhelms the server and can cause it to deny service to valid requests. The above attack is also called SYN Attack.
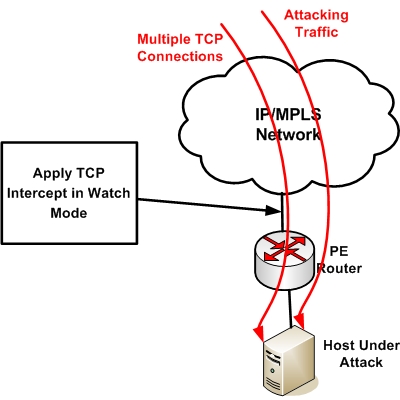
TCP Intercept is a feature on routers used to prevent and mitigate TCP SYN-flooding attacks by monitoring the rate of SYN packets and intervening inside the TCP communication whenever necessary in order to reduce the number of incomplete TCP connections.
There are two modes for TCP Intercept: “Intercept Mode” and “Watch Mode”.
Intercept Mode
The most “invasive” mode is “Intercept Mode”. The router establishes a connection with the client on behalf of the destination server, and if successful, establishes the connection with the server on behalf of the client and knits the two half-connections together transparently. This means that if the connection is legitimate, it will reach the server with no problem. If the connection is from a non-legitimate client, the half-open connection will be dropped by the router. This mode consumes a lot of memory and CPU on the router.
Watch Mode
We recommend using the “Watch Mode” instead of the “Intercept Mode”. In Watch Mode, the router passively watches the connection requests flowing through the router. If a connection fails to get established in a configurable interval, the software intervenes and terminates the connection attempt.
Configuration of TCP Intercept
On router connecting the host under attack, configure the following (assume target host under attack is 1.1.1.1):
Router(config)# access-list 101 permit tcp any host 1.1.1.1
Router(config)# ip tcp intercept mode watch
Router(config)# ip tcp intercept list 101
The above configuration will watch the TCP SYN packets towards host 1.1.1.1. If the SYN packets exceed a certain default value, the router starts to close incomplete TCP connections. Specifically, if the number of incomplete connections exceed 1,100, or the number of connections arriving in the last one-minute period exceed 1,100, each new arriving connection causes the oldest partial connection (or a random connection) to be deleted. These are the default values, which can be altered.
Related Posts
- EIGRP Variance and Unequal Cost Load Balancing in Networking
- Comparison of Reported Distance vs Feasible Distance in EIGRP
- Explanation and Comparison of OSPF E1 vs E2 Routes
- Discussion and Explanation of OSPF Graceful Restart and Shutdown
- Explanation and Configuration of OSPF MD5 Authentication on Cisco Networks