Device virtualization is one of the most popular topics in IT industry today and Cisco has been supporting this concept in the majority of its network devices.
In this article we will talk about Cisco ASA virtualization, which means multiple virtual firewalls on the same physical ASA chassis. Virtual ASA is also known as “Security Context”.
All firewall models (except ASA 5505) support multiple security contexts (i.e virtual firewalls). By default, all models support 2 security contexts without a license upgrade (except the ASA 5510 which requires the security plus license).
Each Context has it’s own configuration file and security policy, i.e. one context is completely isolated and does not depend on other contexts.
The exception is the Admin Context, from which the whole ASA appliance (physical ASA) is managed and also is used to create the other Contexts.
For enabling the creation of virtual contexts on the ASA appliance, we must switch to Multiple Context mode. In this mode some features are not available, like Dynamic Routing, IPSEC and SSL VPN, Multicast and Threat Detection. Let’s make a little discussion when multiple context mode is advisable and when it is not.
When would you want to use multiple security contexts?
● If you want to use the active/active failover feature. Keep in mind that with active/active failover, you should not use more than half of the available bandwidth.
● If you are an ISP and need to offer a different security context for each customer.
● If you need to provide different security policies for various departments, users, or vendors and need to create a separate context for each one.
● If you’d like to reduce hardware requirements by combining the functionality of multiple firewalls into one.
When should you not use multiple security contexts?
● If you need to provide VPN services such as remote access or site-to-site VPN tunnels.
● If you need to use dynamic routing protocols. With multiple context mode, you can use only static routes.
● If you need to use QoS.
● If you need to support multicast routing.
● If you need to provide Threat Detection.
Now let’s consider an example of how Contexts are configured. In the scenario in our topology below, we have one ASA appliance and let’s create two contexts for two customers and one admin context for ASA appliance management.
Configuration of Virtual ASA (Security Contexts)
Physical Topology Diagram:

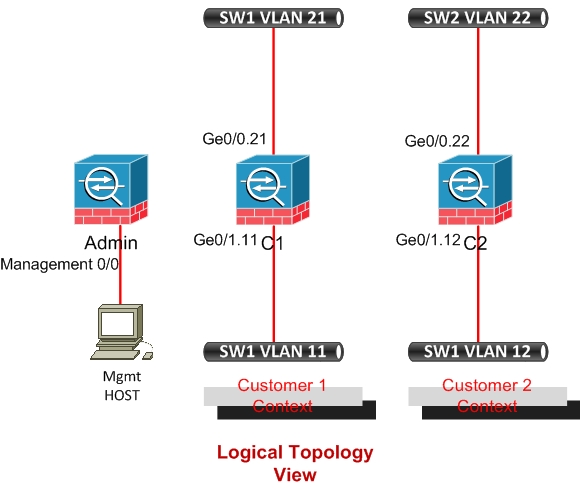
Logical Topology Diagram:
Equipment Used in this LAB
ASA 5520 – Cisco Adaptive Security Appliance Software Version 8.0(3)
Catalyst 2960 – LAN Lite IOS.
Before starting configuration let’s check if it works in Single context mode or multiple context mode. As I’ve already stated, ASA appliance must be in multiple context mode for creating Security contexts.
!Verify ASA Operating mode.
asa # show mode
Security context mode: single
! enable multiple mode, for switching to this Mode, restart is required.
asa(config)#mode multiple
Then the following output is displayed. ASA Appliance converts the current running configuration into two files: a new startup configuration that comprises the system configuration, and “admin.cfg” that comprises the admin context (stored in the root directory of the internal Flash memory).
The original running configuration is saved as “old_running.cfg” (in the root directory of the internal Flash memory).
WARNING: This command will change the behavior of the device
WARNING: This command will initiate a Reboot
Proceed with change mode? [confirm]
Convert the system configuration? [confirm]
!
The old running configuration file will be written to flash
The admin context configuration will be written to flash
The new running configuration file was written to flash
Security context mode: multiple
***
*** — SHUTDOWN NOW —
***
*** Message to all terminals:
***
*** change mode
Rebooting….
Booting system, please wait…
!after rebooting verify ASA Operation mode
asa# show mode
Security context mode: multiple
After restarting let’s start configuration of Contexts. First configure the admin context.
!Configure the admin context
asa(config)# admin-context admin
asa(config)# context admin
asa(config-ctx)# allocate-interface Management0/0
asa(config-ctx)# config-url disk0:/admin.cfg
!configure the Sub-interfaces for Customer1
interface GigabitEthernet0/1.11
vlan 11
interface GigabitEthernet0/0.21
vlan 21
!configure the Sub-interfaces for Customer2
interface GigabitEthernet0/1.12
vlan 12
interface GigabitEthernet0/0.22
vlan 22
Now we start creating contexts for Customer-1 and Customer-2 and allocate interfaces.
! Configure the Customer1 context shown as C1 in diagram.
asa(config)# context c1
asa(config-ctx)# allocate-interface gigabitethernet0/0.21
asa(config-ctx)# allocate-interface gigabitethernet0/1.11
asa(config-ctx)# config-url disk0:/c1.cfg
! Configure the Customer2 context shown as C2 in diagram.
asa(config)# context c2
asa(config-ctx)# allocate-interface gigabitethernet0/0.22
asa(config-ctx)# allocate-interface gigabitethernet0/1.12
asa(config-ctx)# config-url disk0:/c2.cfg
I will not describe how VLANs on Switches are configured. Let’s consider switching between Contexts. We can switch to any context from admin context, but we can’t switch from Customers context to anywhere.
! Let’s log in to Customer1 context. The syntax of command is the following:
changeto context <context name>
asa#changeto context c1
! Let’s switch to system configuration mode. Switching to this mode is available only from Admin Context. In system configuration mode Contexts are created and resources are allocated.
asa#changeto system
Related Posts
- Prevent Spoofing Attacks on Cisco ASA using RPF
- Configuring Connection Limits on Cisco ASA Firewalls – Protect from DoS
- Configuring AAA Authentication-Authorization-Accounting on Cisco ASA Firewall (TACACS+, RADIUS)
- Cisco ASA Firewall Management Interface Configuration (with Example)
- How to Configure Access Control Lists on a Cisco ASA 5500/5500-X Firewall (with Examples)