In the fields of Information Technology, cybersecurity, computer networking etc, having visibility in your systems and networks is essential in order to detect security risks, prevent or fix faults, optimize performance etc.
This visibility and information is usually provided by the logs generated by your I.T systems and infrastructure.
Because of the enormous amount of logs and info generated by I.T systems and networks, businesses and other organizations have their hands full with more data than they know what to do with.
This makes tools and platforms that organize, analyze, and catalog log data essential.
Nowhere is that truer than within the realm of technology infrastructure maintenance and cybersecurity.
There, operators and IT professionals have to deal with multiple streams of real-time data coming in the form of system logs, application data, and other types of telemetry.
Moreover, they need the capacity to extract useful information from all that data and the ability to translate it into visualizations and reports that those outside of their IT organization can understand.
That’s where tools for log analysis and observability like Splunk enter the picture.
Splunk is an enterprise-grade data monitoring, analysis, and reporting platform used by 92 of the firms on the Fortune 100 list.
That makes Splunk one of the most popular and trusted software tools in log analysis, observability, and security incident event management (SIEM) systems.
However, it’s by far not the only tool available and can be complex to learn with a high price-tag associated with it in terms of cost.
Businesses looking to build a toolset in those areas do have quite a few alternatives they can use instead.
To elaborate, in this article we present twelve of the best alternatives to Splunk for log analysis, observability, and SIEM purposes.
Please note that the list below is in no particular order.
1. Graylog
Graylog is a well-known SIEM and log-analysis tool that makes an excellent alternative to Splunk.
This is due in large part to their overlapping feature sets. Both aggregate unstructured and structured data into a single unified data structure and provide monitoring, alerting, and reporting capabilities.
For its part, Graylog can collect log data from different types of sources (such as syslog from network devices, logs in text format, logs within databases etc) and aggregate all these data into ElasticSearch for its search functionality.
Beyond that, it comes with a few main features that make it a viable alternative to Splunk, including:
- A built-in query builder
- A built-in data viewer
- Log collection and consolidation capabilities
- Support for multiple Log types (structured, unstructured data etc)
- An available free and open-source version
That last point makes Graylog especially attractive to businesses. It means that they can use Graylog’s free version to build their own customized data analysis dashboards as they see fit.
It’s also worth pointing out that the free version comes with 10 of the 18 core features found in the paid versions of the software.
That makes them almost as powerful as those paid versions, called Graylog Operations and Graylog Security, respectively.
Plus, the versions are interoperable, should any free version user find it necessary to upgrade to a paid edition at any point.
What’s most appealing about Graylog, however, is its thriving user community. Within it, users share countless content packs that can help other users add prebuilt functionality to their own Graylog instance.
This ready-made resource makes it easy for businesses to get up and running with Graylog and begin deriving useful insights from it almost immediately.
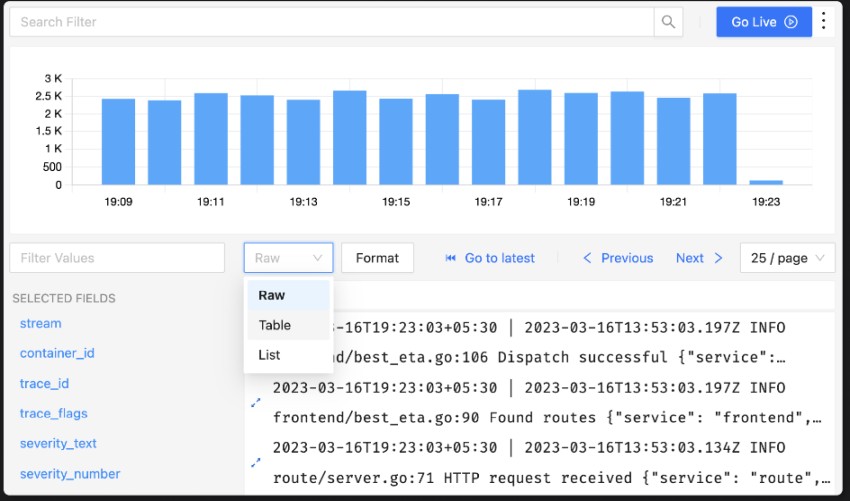
2. Grafana Loki
Grafana Loki is another alternative to Splunk. However, it’s not a tool aimed at large enterprise cases that require full log indexing and storing.
Instead, Grafana Loki does not index or store the full text of data logs, rather it just indexes the metadata of the log files.
Instead, it’s primarily geared toward smaller to medium businesses that don’t require much log analysis and storage requirements, compared with Splunk’s nearly unlimited capabilities.
The main strength of Grafana Loki is its simplicity, which makes it a breeze to get up and running within a variety of infrastructures.
Also, Grafana Loki works with an impressive array of infrastructure types, owing to its compatibility with a panoply of logging clients.
Users can choose from the native Grafana Agent, as well as Vector, Fluentd, Logstash, Fluentbit, and Promtail as their needs dictate. Because of that, it’s hard to find a system type whose logs you can’t easily ingest into Grafana Loki.
Best of all, though, Grafana Loki is open-source and free to use. Like Graylog’s free version, that makes it a great tool for businesses that wish to build a flexible SIEM or log visibility solution tailored to their needs.
While not as robust on the reporting side of the equation as Splunk, the system’s built-in LogQL query language means there’s no end to the kinds of customizations users can create.
3. ELK Stack
While not an exact analog for Splunk, ELK Stack is nevertheless a popular alternative for it.
That’s partly due to it including and building upon Elasticsearch, which forms the core of some of Splunk’s most important functionality.
In addition to Elasticsearch, ELK Stack bundles two more open-source projects called Logstash and Kibana.
Together, the three provide log ingestion, cataloging and search, and powerful data visualization capabilities.
More recently, ELK Stack has added an array of new features and began the process of rebranding, taking on the name Elastic Stack to reflect its new capabilities.
ELK Stack’s strength, unsurprisingly, is its search capabilities. That makes it a powerhouse for organizations that need to catalog vast amounts of data and recall specific bits at will.
However, compared to the other alternatives listed here, Elk stack isn’t as new-user friendly.
Its query language is difficult to master, but doing so helps users unlock the platform’s massive data analysis potential. On top of that, it’s not as simple to get up and running as some of the other options.
4. Mezmo Log Analysis
Another highly-regarded alternative to Splunk is Mezmo Log Analysis. Working synergistically with Elasticsearch, it’s another powerful log aggregator with powerful cataloging and search capabilities.
Using the so called “Telemetry Pipeline” component, this product collects, transforms and routes data to destinations that can store or analyze the data, such as Elasticsearch, or even to cheap storage devices for archiving.
Like the other options covered here, Mezmo Log Analysis features broad compatibility with most log-producing hardware and software.
Plus, it boasts especially flexible deployment options, including on-premises and public/private/hybrid cloud options, too.
Mezmo Log Analysis comes in three flavors. There’s a free community-supported edition, as well as Professional and Enterprise paid tiers.
Critically, the platform relies on a pay-for-what-you-use pricing model, which makes it especially flexible for businesses with budgetary constraints.
On all three flavors, though, users get a variety of useful features, including live tailing of logs, alerting, visualization, and a flexible query builder.
That makes the platform great for building custom dashboards, graphs, and other data views.
5. Grafana Cloud
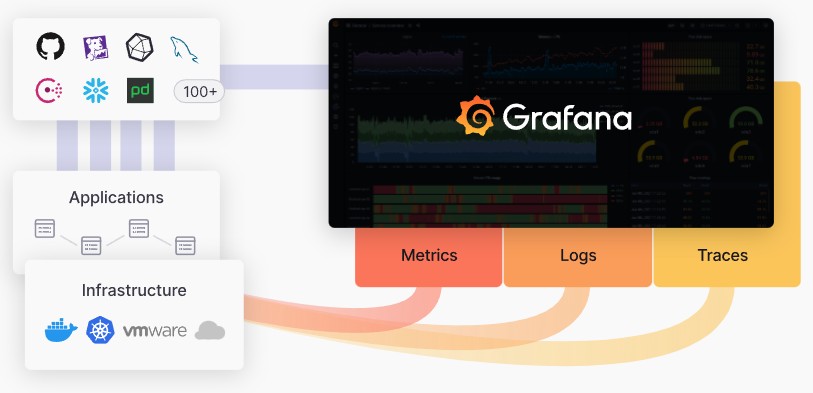
A close sibling of Grafana Loki, Grafana Cloud is a fully-managed cloud-based alternative to Splunk.
Where Grafana Loki caters to simple on-premise logging aggregation for small to medium companies, however, Grafana Cloud aims to function as a full managed and cloud-based solution for log data observability.
To that end, it features a near-endless list of native pre-built integrations that make ingesting data from popular platforms almost plug-and-play.
Plus, Grafana Cloud builds on one of its parent company’s strengths (Grafana), offering some of the most flexible and powerful visualizations and reporting tools on the market.
Plus, as a managed platform, Grafana Cloud eliminates the need for businesses to support any new infrastructure or add any new support capabilities.
6. Sumo Logic

Another excellent Splunk alternative with similarities in all the right places is Sumo Logic. It shines in the areas of observability and security monitoring and is also a cloud-native platform.
For example, both tools make for powerful SIEM tools capable of spotting advanced threats. These include insider threats, external attacks or intrusions, and advanced persistent threats that burrow into protected systems and remain for long periods.
Perhaps the most powerful indication of Sumo Logic’s place within log analysis and collection platform hierarchy is its client list.
Like Splunk, Sumo Logic has a long list of well-known clients, including Whole Foods, Pitney Bowes, and Samsung, among others. However, Sumo Logic does differ from Splunk in that it’s a cloud-only solution and offers no on-premises deployment option.
Like Splunk and Graylog, however, Sumo Logic also benefits greatly from a vast library of available pre-built integrations, known as apps in Sumo Logic parlance.
Those apps make pulling useful insights from varied data quicker than it would be with most other observability tools. Plus, Sumo Logic’s flexible logging agent makes integration with existing systems fairly straightforward, too.
Sumo Logic also claims significant cost reduction since its licensing is based on average monthly data ingest, supporting 30% more data than models based on daily peaks.
7. Logz.io

Logz.io is another amalgam of open-source tools that’s all but identical to ELK Stack. As such, it has a similar feature set to ELK Stack, making it an excellent alternative to Splunk.
The principal difference is that Logz.io only offers a managed SaaS solution that runs on its own cloud infrastructure. They offer both an “Observability Platform” and “Security Platform”.
That makes it a great SIEM and log monitoring tool for companies that don’t want to roll their own systems, as it also comes with 24/7 support.
The main drawbacks to Logz.io include some scalability concerns, as some customers report query slowness at peak traffic times.
Plus, some users chafe at the event restrictions imposed by the service’s catch-all subscription plans. However, Logz.io is difficult to beat for businesses that want a turnkey log observability or SIEM solution and for whom budget is also a concern.
In fact, Logz claims that their plans are far more cost efficient than Splunk’s, with pricing based on volume of data ingested into the system.
8. Wazuh
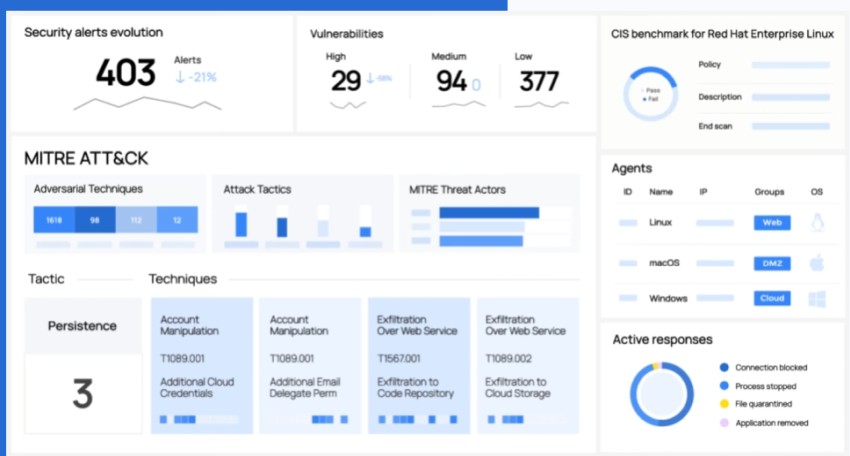
For users that need a platform focused on security and SIEM that isn’t able to accommodate as many data types as Splunk, there’s Wazuh.
It’s purpose-built for security analytics work rather than as a catch-all data and log analysis solution.
As such, it also includes an endpoint security module that provides threat prevention, detection, and response capabilities (XDR).
In fact, this laser focus on security concerns often sees companies deploying Wazuh in tandem with Splunk, using the latter’s data collection and visualization capabilities to integrate Wazuh into a larger and more varied data infrastructure.
However, on its own, Wazuh also offers excellent data dashboards and visualization capabilities, as well as a suite of tools to help organizations ensure compliance with major regulatory schemes like the GDPR and HIPAA.
9. Loggly

Loggly comes from the well-known I.T monitoring company Solarwinds and is a cloud-based log management SaaS solution.
Like Splunk, Loggly is a tool built to provide businesses with advanced log monitoring and analysis capabilities for application analytics, and alerting, log insights etc.
Loggly integrates with most types of log-generating hardware and software and centralizes their data into a single intuitive interface.
Critically, Loggly boasts faster complex search capabilities than Splunk, which excels at quick, simple, time-limited searches instead.
That’s due in part to Loggly’s use of Elasticsearch and its proactive log parsing that identifies key data fields prior to indexing.
Loggly also uses a feature called Dynamic Field Explorer that helps users maintain a high-level view of interconnected data, functioning as a map of real-time events logged by the system.
10. SigNoz
SigNoz is another popular open-source alternative to Splunk. It’s billed as a full-stack observability and performance monitoring system that features log aggregation, alerting capabilities, traces, and metric collection.
Plus, SigNoz is a self-hosted solution, making it a good option for businesses that either can’t or don’t want to entrust their data to third parties on the cloud.
If there’s any feature that sets SigNoz apart from many log observability tools, it’s the compliance with OpenTelemetry data standard.
It’s a vendor-agnostic instrumentation library that’s fast becoming the de-facto industry standard for telemetry data generation and sharing.
In other words, SigNoz can already share data with a growing ecosystem of other SIEM tools and platforms that other options would need customization to achieve.
11. Datadog
Datadog is a SaaS analytics and tracking platform that offers businesses another alternative to Splunk.
It’s a favorite option of cloud-native companies because of its heavy emphasis on cloud compatibility.
Like Splunk, though, Datadog boasts a feature set that goes well beyond simple log aggregation and search. As such, it has a variety of use cases, including:
- Monitoring digital user experiences
- Security monitoring and analytics
- DevOps monitoring automation
- Realtime business intelligence
- Shift-left testing
All told, Datadog features over 250 built-in tools that make it one of the most flexible solutions on this list.
It’s also one of the simpler solutions to get up and running, although users do tend to chafe at the platform’s pricing and difficulty with scaling.
12. New Relic
The final entry on our list is New Relic, an all-in-one observability platform built to meet the needs of modern companies.
While it isn’t a full-featured SIEM solution like some of the other options above, it does offer a robust feature set aimed squarely at DevOps engineers.
For example, it features monitoring capabilities that go deeper into the various aspects of the virtual environment than similar solutions.
It also has a host of plugins that help it integrate with major web technologies like NGINX, HAProxy, MySQL, and Amazon’s AWS platform. It even boasts a built-in generative AI observability assistant, which is a unique feature among its peers.
Related Posts
- The Elusive Search for the Ideal Network Monitor Tool and How it Can be Easier
- Unveiling the Significance of Network Automation in Contemporary Networking
- 13 Top Open Source Port Scanners for Windows for Host Discovery
- 15 Best Firewall Management Software Tools for Rules and Policies
- 11 Alternatives to Solarwinds NPM for I.T and Network Monitoring