The Cisco ASA 5505 firewall is an excellent device for small branch office locations since it can offer several network services in one box.
It can provide firewall security, IPSEC VPN lan-to-lan connectivity with a central office, and even power-over-ethernet connectivity for local IP phones (two of its network interfaces are power-over-ethernet ports).
A common network scenario using Cisco ASA firewalls is usually found in Enterprises with small branch offices that implement a Cisco IP Telephony Voice over IP solution.
Typically, a Cisco CallManager at the Enterprise central office is used to control Cisco IP Phones at small branch offices.
This implementation allows centralized call processing, reduces the equipment required, and eliminates the administration of additional Cisco CallManager and other servers at branch offices.This is illustrated in the diagram below:
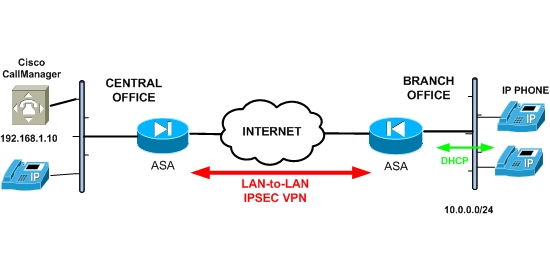
The DHCP feature of the Cisco ASA 5505 firewall can be used to assign IP addresses to the Branch Office IP phones.
Via the DHCP, the ASA Firewall can also provide to the phones the IP address of a TFTP Server (this is usually the CallManager server itself).
Cisco IP Phones download their configuration from a TFTP server. When a Cisco IP Phone starts, if it does not have both the IP address and TFTP server IP address preconfigured, it sends a request with option 150 to the DHCP server (Cisco ASA 5505 in our case) to obtain this information.
In our example above, the Cisco ASA firewall will assign IP addresses in the range 10.0.0.0 and also provide a TFTP server IP address of 192.168.1.10 (CallManager at the central office).
After the IP Phones obtain this information, they will be able to communicate with the central CallManager through the IPSEC VPN tunnel.
To configure the DHCP Option 150 on Cisco ASA:
ASA(config)# dhcpd option 150 ip 192.168.1.10
ASA(config)# dhcpd address 10.0.0.10-10.0.0.20 inside
ASA(config)# dhcpd enable inside
Related Posts
- Prevent Spoofing Attacks on Cisco ASA using RPF
- Configuring Connection Limits on Cisco ASA Firewalls – Protect from DoS
- Configuring AAA Authentication-Authorization-Accounting on Cisco ASA Firewall (TACACS+, RADIUS)
- Cisco ASA Firewall Management Interface Configuration (with Example)
- How to Configure Access Control Lists on a Cisco ASA 5500/5500-X Firewall (with Examples)