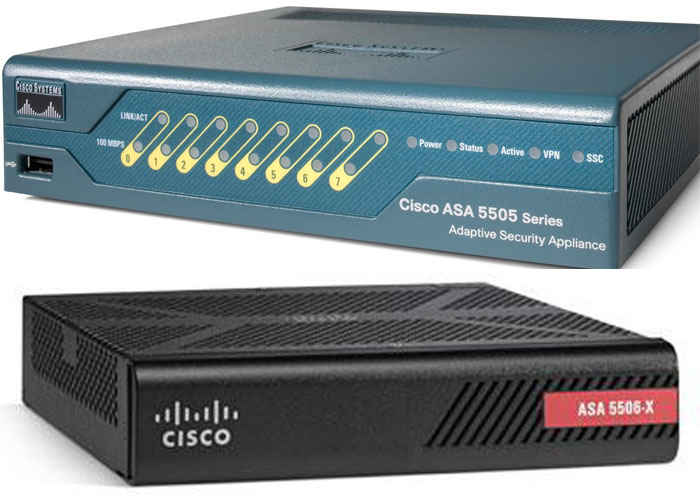
The new ASA 5506-X and 5508-X were released a few months ago from Cisco and are the models which will replace the very successful ASA5505 SOHO firewall.
Especially the 5506-X is marketed as the ideal replacement for the 5505 which was very popular and successful in small network deployments.
As you might know already, the 8 interfaces of the ASA 5505 act as an 8-port Layer2 switch (with Power of Ethernet ports as well). This means that you can directly connect computers and other hosts on the 8-port switch of the firewall device without requiring an additional Layer2 switch in the network. This is particularly useful in very small SOHO networks with 4-5 devices (such as small remote offices or very small business networks). If you had also the security plus license, you could further separate the 8-ports of the 5505 into additional VLANs.
Now, the new ASA5506-X does come with 8xGE gigabit interfaces which however are routed interfaces. In simple words, there is NO switch on the ASA 5506-X !!!
This means that you need to have an external layer2 switch in order to connect several devices on the network. If you want to have a similar situation as the 5505 where all the ports from 1 to 7 were assigned in Vlan1 as “inside” security zone, then you need to configure etherchannel (or port-channel as Cisco defines it). Basically you group together several ports of the 5506-X and you create a logical port-channel interface which you assign it as the “inside” zone.
Despite the fact that there is no embedded switch on the 5506-X, this device has a lot more security features and much better performance than the 5505 which compensates for the lack of a switch. If you enable the FirePower subscription features on this device, then you have an all-in-one security solution which will greatly help in defending against cyber attacks. Have a look at this ASA 5506-X Configuration Tutorial for basic and advanced examples of configuring this new firewall model.
Related Posts
- What is Cisco ASA Firewall – All you need to Know
- Traffic Rate and Bandwidth Limiting on Cisco ASA Firewall
- Cisco ASA Firewall (5500 and 5500-X) Security Levels Explained
- Cisco ASA 5505-5510-5520-5540-5550-5580 Performance Throughput and Specs
- Password Recovery for the Cisco ASA 5500 Firewall (5505,5510,5520 etc)